6 Questions To Ask for Protecting Student Data in Distance Learning

By: Nightfall Editorial Team
The education industry is facing a massive wave of changes as instruction moves online en masse. The response to the Coronavirus pandemic has placed a strain on schools and teachers since the spring, when everyone was suddenly asked to attend and teach classes online.
Like any industry that is asked to rapidly adapt to a new environment, schools and educators are struggling to keep up with data privacy and cloud security standards. But even before the pandemic hit, student data and school technology systems weren’t as safe as they could have been.
A 2019 report from Help Net Security found the following data of the pre-pandemic state of cybersecurity among schools:
- 71% of organizations that were breached in the previous year never classified all the data they store in the cloud.
- 65% of organizations say business users were responsible for the incidents.
- Only 19% of educational institutions are ready to move their entire infrastructure to the cloud, down from 32% in 2018.
Tech and security decision makers working to protect schools should ask six main questions to diagnose their organizations’ readiness to move instruction online, identify gaps, and find solutions to their most pressing issues in student data security. We’re breaking down each of these questions and providing some insight into how to approach the biggest problems that educational tech leaders face, in the best and worst times alike.
Question #1: Is my school or district FERPA compliant?
This is the most important question to ask of your entire organization. The discovery you’ll gain from the answers to this question will diagnose the security problems you’re facing, and help you determine where to put your resources.
FERPA stands for the Family Educational Rights and Privacy Act of 1974 (also known as the Buckley Amendment). It’s a U.S. federal law that protects the privacy of student educational records. As those records include personally identifiable information (PII) of underage students as well as adults over 18 who are enrolled in educational programs, improper data exposure under FERPA can spell big trouble for schools and districts who don’t enforce proper security policies.
Solution: Examine your cloud security posture to determine where the compliance blindspots could be. This can include misconfigured cloud drives or expired security certificates that can leak data without you even knowing about it, or tools and resources that don’t adhere to FERPA standards. Zoom took steps to become FERPA-compliant as early as February 2018, which likely led to the video conferencing platform becoming a popular choice when COVID-19 forced schools around the U.S. to begin remote instruction. If FERPA compliance isn’t 100% clear for a system, app, or platform, it’s best to question its viability within your organization.
Question #2: Are the third and fourth party vendors we work with secure?
We’ve mentioned before how third and fourth party vendors can be a source of data leaks in an organization. Schools face this problem in many of their partner and vendor relationships. Under the FERPA, data exposure like this isn’t just a PR nightmare — it’s breaking the law.
LeRoy Rooker, senior fellow at the American Association of Collegiate Registrars and Admissions Officers, is a FERPA expert. He was featured in an interview with EdSurge about the dangers of data exfiltration in school technology systems, and the unique ways in which schools and districts are held responsible for any improper use or access of data by third or fourth party vendors.
Under FERPA, schools are responsible for what their vendors do with data. That means that if a vendor intentionally or accidentally misuses students’ education records, the school would still be at fault.
Higher education institutions are in the hot seat over data exposure or other unsafe security conditions due to relationships with vendors:
- Salon reported that last month, the University of California (UC) made a commitment to invest $200 million in investment firm Thomas Bravo that could include access to massive amounts of student data through a subsidiary. The move prompted more than 50 people who work at colleges to sign a public letter urging Thomas Bravo to issue a legally-binding statement promising that it would not abuse its newfound access to student data.
- The University of York experienced a potential event when their third-party computing provider Blackbaud underwent a ransomware attack. University of York student data like names, dates of birth, student ID numbers, phone numbers, email addresses, and physical addresses were among the business-critical data at risk.
Solution: Vet all third-party resources thoroughly before entering into contracts and business agreements. Be especially wary of any resource that’s free. As Steven McDonald, FERPA expert and general counsel at the Rhode Island School of Design points out, “free” vendors don’t charge a usage fee to institutions, but their business model typically entails data mining, which is not allowed under FERPA.
Question #3: Are we using the highest standards of encryption on our databases, systems, apps, and other tech tools?
Encryption is a chief concern for tech leaders. Strong encryption will protect data as it moves across your entire organization. As schools and districts are using more cloud apps to communicate across their organization and facilitate remote instruction, data moving around these new infrastructures must be guarded with the highest possible levels of security. A few acronyms to know are AES and TLS. These two are the backbone of protecting data in motion, with AES 256 and TLS 1.2 as high standards for encrypting and securing data traveling within a cloud connection. Failure to properly encrypt data in a cloud system can cost your school a lot of time, money, and lost trust, plus dealing with the fallout from violating FERPA and other regulations. Solution: Do a frequent audit of your organization’s cloud network and apps. Constantly check up on the TLS and AES standards and correct mistakes as soon as they’re found. It’s important to keep in mind the limitations of TLS especially — while it’s excellent at protecting data in motion, it’s not built to secure data on end systems.
The health of your cloud systems and cloud-based apps relies on ensuring the secure delivery of data over the Internet without possible exposure or alteration.
Question #4: Which cloud-based tools are we using, and are they secure?
Tools and platforms can vary across schools, even within the same district. Functionality is typically the first question that comes up when vetting a potential new tool to use for remote instruction. Unfortunately, security is either a secondary concern, or not considered at all.
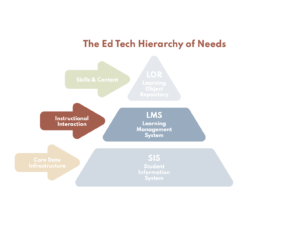
It’s important to also expand your knowledge of which platforms, tools, and apps are under the cloud security umbrella. Some aren’t readily apparent as potential data loss vectors — even tools like learning management systems (LMS) where teachers post instructions, assignments, and links to resources for students and parents to access, or communication tools for emails or newsletters can be unsafe if they aren’t secure.
Solution: As mentioned above, Zoom has made its FERPA compliance for video conferencing in schools very clear. When the tools your school or district uses are less transparent about security policies and protocols, there’s a few things to look for when assessing how it fits (or doesn’t) into your security posture:
- Encryption: Does the tool list TLS and AES as protecting data in transit?
- Sharing settings: Does the platform contain a privacy policy or other language that states they don’t share customer data with third parties?
- Data storage: Does the app store customer data other than account information, like email address, first and last name, etc.?
- Information or account retention: What length of time does the tool retain accounts for? Does account retention solely assist with reactivation or login issues?
Data loss risk rises with every unsecured portal, app, and tool within your organization. It pays to be skeptical of tools that don’t look safe on the surface. Always check under the hood to ensure optimal security standards.
Question #5: What other data privacy laws and regulations should my school or district be following?
FERPA isn’t the only data security framework that schools must follow. Other laws and regulations that concern student data and aim to protect underage people from having their information shared improperly are also often applied in data security for schools and districts, like COPPA and PPRA.
The Children’s Online Privacy Protection Act of 1998 (COPPA) is a U.S. federal law that protects the privacy of children under 13 years of age. The Protection of Pupil Rights Amendment (PPRA) of 1978 (also known as the Hatch Amendment) is a law intended to protect the rights of pupils and the parents of pupils in programs funded by the U.S. Department of Education.
Both laws include strict requirements about parental notice and consent on how underage students’ data should be gathered, used, and shared within an organization. Complying with these and other regulations is essential for securing your school or district.
Solution: Even with FERPA, COPPA, and PPRA compliance under control, your organization might still have some security gaps. The watchdog group Parent Coalition for Student Privacy has a wealth of information and resources to help parents and educators create safer digital environments for students.
One of their most useful tools is the State Student Privacy Report Card. The most recent report, published in January 2019, ranks all 50 U.S. states based on grades earned in seven key data privacy categories:
- Parties covered and regulated
- Transparency
- Parental and student rights
- Limitations on commercial use of data
- Data security requirements
- Oversight, enforcement, and penalties for violations
- Other provisions
The bad news is that over half of U.S. states scored at D+ or lower among these criteria, and 11 states have no sufficient privacy regulations in place or enforced. Just four states ranked at B-minus or higher, and the best performing state (Colorado) scored only a B.
The State Student Privacy Report Card is a diagnostic tool for how insidious the data security problem is among schools and districts. Hopefully this resource and others available from the Parent Coalition for Student Privacy can help education security professionals in their quest to build safer cloud systems to keep students secure online.
Question #6: How well do we really know our school or district security posture?
After going through the first five questions, the answer to how well you know your organization’s security posture should be clearer than ever. You’re more likely to understand which tools are safe and how to avoid unsecure apps. You have more information to determine where your school or district stands on federal, state, and local laws. The work is just beginning.
A comprehensive cloud security checkup for your school or district includes looking into other questions not covered by deep dives on compliance, tools, or encryption. It’s time to build a solid foundation for cloud security within your organization by interrogating the general oversight and awareness of security and data protection among your teams.
Solution: Create a list of questions that aim to find any weak points in your cloud security chains. Engage with different departments and leaders around the organization, as their perspectives might help you find flaws you missed the first time around. To help you get started, here’s a quick list of questions that can lead to cloud security enlightenment:
- Are we prepared for a security breach or data loss event?
- Have we conducted a Privacy Impact Assessment (PIA)?
- Have we classified our data according to risk: high, medium, and low?
- Who has access to our various data assets? How can we monitor these actors and control their access?
- How are we capturing data? Do we have the right level of consent?
- Do we have a way to monitor and detect security incidents continuously?
If the answers to these questions are ambiguous or insufficient, you’ll know where you need to do the most work. Data security for education providers is a massive undertaking. Thorough and deliberate examinations will help you achieve the highest level of security for your organization.
An Education in Cloud Data Security
The spring term has come and gone, with lessons to be learned from widespread online deployment of instruction and interactions between students and teachers. As summer turns to fall and the start of another school year looms, it’s clear that COVID-19 will keep students at home for a while. To help teachers provide much needed educational continuity, and to keep students safe while they learn, education technology security professionals must uphold the highest standards of data security for the cloud platforms, tools, and apps used within the virtual classroom. This list of questions is the best place to start to achieve the cloud security goals for your organization.
About Nightfall
Nightfall is the industry’s first cloud-native DLP platform that discovers, classifies, and protects data via machine learning. Nightfall is designed to work with popular SaaS applications like Slack & GitHub as well as IaaS platforms like AWS. You can schedule a demo with us below to see the Nightfall platform in action.
For more, see:
- How to Stay Secure When Teaching Remotely
- Cybersecurity: A Promising Approach to Integrating CompSci and PBL
- Choosing the Right Tools for Remote Learning
This article was originally posted on Nightfall.
Stay in-the-know with innovations in learning by signing up for the weekly Smart Update.






0 Comments
Leave a Comment
Your email address will not be published. All fields are required.